Convert is the Most Privacy Focused Testing Tool on the Market. Here’s Why
We have been improving outcomes for a decade now.
And with over 30 billion experiences tested, we’ve perfected a tool that drives improved conversions for customers from all possible industries – without hassles.
But when the GDPR tidal wave hit, we wanted to go beyond improving outcomes.
We wanted to be the optimization tool for savvy users in a world where privacy concerns are going to grow only more important with each passing year.
It took the better part of 8 months, thousands of hours, hundreds of (tiny) arguments but we managed to accomplish everything we wanted to.
Everything that you need to run tests and mine insights, without disregarding GDPR or the ePrivacy Regulation.
Table of Content:
In-App Updates: Balancing Privacy & Features
Anonymization of Visitor’s ID: Test without Consent in Our Default Mode
An important principle in the European Union’s General Data Protection Regulation (GDPR) (Chapter 2, Article 5) is data minimization.
This means that in the context of personal data, product and service providers should only collect, store and process what is adequate, relevant and limited to their business case.
There is no clear definition of what personal data should be collected and what should not be. It is completely based on the specific use case.
To practice data minimization principle, we anonymized visitor’s ID in our tracking by grouping hundreds of website visitors into visitor groups that only count the presence of the visitor.
Individual visitors are not stored in Convert Experiences. It will not be possible to reconnect group counts to individual visitors in any way.
GDPR provided us an opportunity to take a hard look at what we were storing in Convert and what the use case was for keeping it in an increasingly privacy-centric environment.
Removal of transaction IDs: Getting “Push”
We also changed our revenue tracking to use pushRevenue instead of sendRevenue.
- pushRevenue does not send any transaction IDs.
- sendRevenue sends the transaction ID but is ignored and not stored.
<script>
window['_conv_q'] = window['_conv_q'] || [];
window['_conv_q'].push(["pushRevenue",revenue,products_cnt,goal_id]);
</script>Persistent Cookie Expiration: You’re Great But We’ll Remember You Only for 6 Months
Persistent cookies are placed on a user’s computer when they first log on to a website and remain on that computer even after the user moves away from the site and closes the browser.
These cookies have taken on the name “tracking cookies”, as they are often used by advertisers to track a site user’s movement across multiple web pages and create targeted advertisements based on user browsing and search patterns.
Each persistent cookie has a name and an expiration date set by the creator.
When a website sends a cookie, it asks your browser to keep that particular cookie till a certain date and time has passed.
According to the recommendation of the ePrivacy Directive, persistent cookies should be deleted every 12 months at least, but unfortunately most are stored a lot longer than that.
In Google Adwords a cookie may last up to 540 days and in Google Analytics a cookie may last up to 2 years. Examples have been registered of cookies that were made to have a lifespan of +7000 years!
Persistent cookies can be easily misused and there is a lot of concern around this eventuality. Indeed, Yahoo revealed that the reported hacks of its servers included stolen and forged cookies that allowed the hackers to access user accounts without the need of a password. This means hackers were able to copy the persistent cookies located on Yahoo’s servers, create forged versions of them, and then access user accounts with little effort.
To respond to this privacy challenge, we at Convert implemented a reduction of the persistent cookie lifetime storage limit from 12 months to 6 months.
Removal of Third Party Cookies: We’re Not “Talking” to Them
A third-party cookie, is a cookie that (a) comes from a different domain, or (b) is “set by a data controller that is distinct from the one that operates the website visited by the user.”
You can install a program called Lightbeam on your FireFox browser which lets you see all the third party cookies downloaded in the shadows of your web browser. Here are my results for my commonly visited sites:
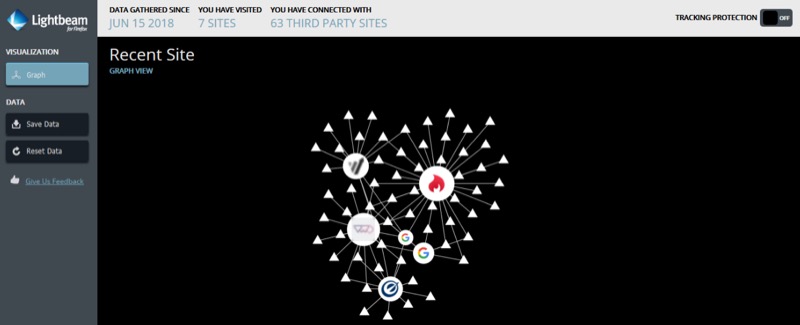
As you can see in the screenshot above, my browser has literally become a cookie jar – just after visiting 7 websites.
Sites often signal your visit to third party platforms and share your browsing data with them for advertising and marketing benefits.
Cookies have received a lot of attention under the ePrivacy Directive because they not only track information but can indeed steal information.
The nature and process of being tracked by third parties create a conflict of interest between users and website owners, particularly when third party cookies from on-site ads are involved.
If your site uses third party cookies or allows their use, you expose yourself to more consequences under the cookie law.
To ensure complete customer and visitor privacy, as of February 21st 2018, we disabled all third party cookies.
We Got Your Back: Convenient GDPR Warnings!
We introduced warnings to inform our customers of GDPR-related settings or options used in their Projects or Experiments:
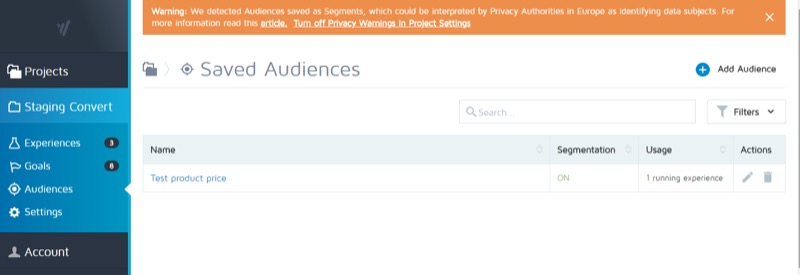
- Convert Experiences has traditionally allowed the grouping of site visitors by conditions like location and behaviour. These groups are referred to as custom segments. However post GDPR, if the Segmentation feature is enabled, this can be interpreted by Privacy Authorities in Europe as a way to identify data subjects. To inform users we have inserted conspicuous warnings that activate if segmentation is enabled for at least one audience.
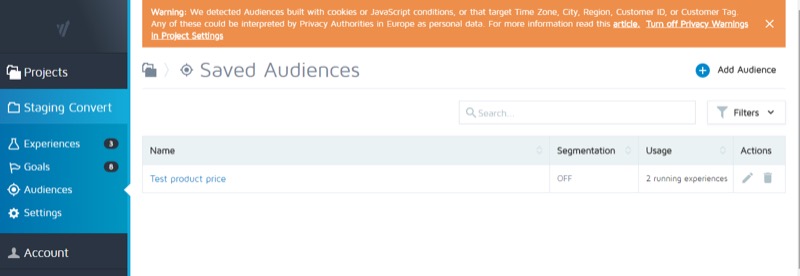
- Audiences built with Personal Data: A GDPR Warning exists in Saved Audiences and on the Experience Summary pages when Audiences are built with cookies or JavaScript conditions, or if Time Zone, City, Region, Customer ID, or Customer Tags have been targeted:
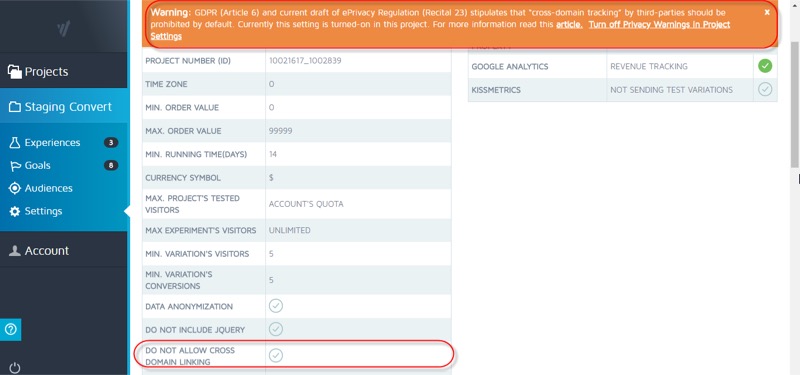
- Cross Domain Tracking: The cross domain cookie is by default turned off for all projects in Convert Experiences. Turning it on activates another warning:
- Personalization Experiences may contain small segments (under 100 unique visitors) and this may be interpreted by Privacy Authorities in Europe as identification of data subjects. For that reason, we’ve added a warning to the summary of any Personalization Experience.
The purpose of these warnings is to ensure that our users understand which features may be viewed as potential “identification” of data subjects by EU authorities.
It is difficult to memorize a gist of the GDPR mandates and the ePrivacy directives!
By using Convert Experiences you work with a tool that can do a lot, but also punctuates it’s potential with reminders that certain actions are now interpreted differently in European Union countries.
You have the ability to turn off GDPR warnings.
Login Server: Frankfurt, Germany It Is
Another big change GDPR has ushered in has to do with the location of data storage.
This one is simple.
If you store data of EU citizens, the data should remain on EU soil. In other words you need to have servers in European Union countries.
Data should not be sent to servers outside the EU (to the US, for example), under any circumstance.
We moved our login server from the US to a data center in Frankfurt, Germany that is powered by carbon neutral energy.
DNT Setting: Your Browser Speaks, We Listen
Do Not Track is a technology and legal framework that enables users to opt out of tracking by ad-networks, analytics services, and social platforms.
DNT empowers traffic with the power of choice.
It’s a feature in web browsers that allows users to express their preference for not being tracked to the web sites and services they use every day.
The EU GDPR enforces the respect of this new browser preference. Combined, the technology and law provide a viable path forward to reclaim the right to privacy on the web.
DNT is a user making an explicit feature request, I do not want to be tracked. DNT is a user preference that forces the browser to send an HTTP request to the server explicitly telling that server not to track user behaviors.
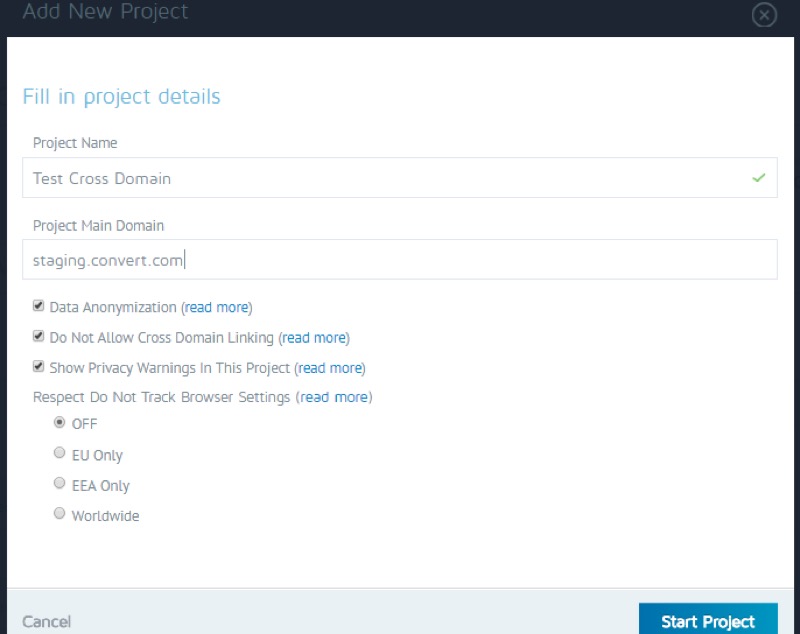
We’ve added configurable support for Browser “Do Not Track” settings by Project.
By default, the OFF option is selected when you create a new Project, but you may choose from any of the following settings:
- OFF
- EU Only
- EEA Only
- Worldwide
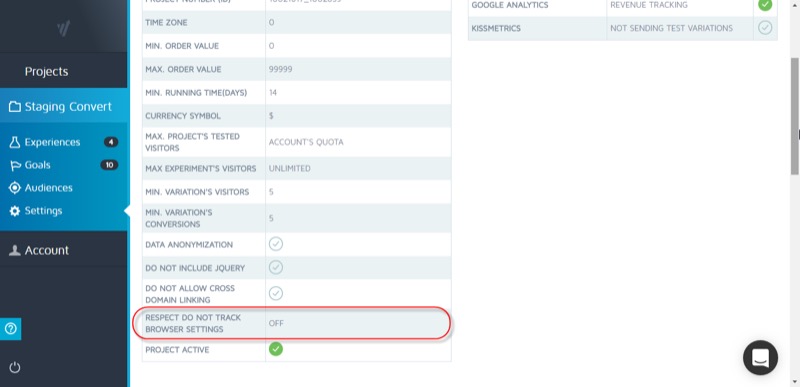
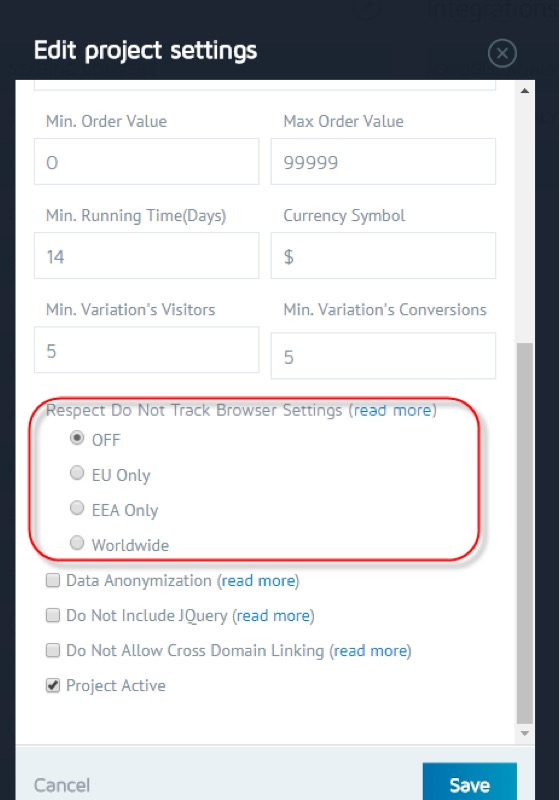
In short we allow our users to steer clear of counting or in any way using the data of individuals who prefer not to be tracked.
Learn more about this new feature here.
Opt Out: One Link to Exclude Them All
There are two sides to the tracking story.
One, savvy website visitors can choose to enable Do Not Track on their browsers and hide from prying eyes.
Two, they should have the power to opt out of tracking directly from the websites they visit.
We at Convert know that and have placed the opt-out feature https://www.convert.com/opt-out/ on the Convert app settings page.
With just one click on the Opt-Out link, visitors can choose to opt out of being tracked by all websites that use the Convert Experiences app.

Cross Domain Testing: Disallowed by Default
Cross-domain tracking makes it possible for Convert Experiences to see sessions on two related sites (such as an ecommerce site and a separate shopping cart site) as a single session. This is sometimes called site linking.
Suppose you have an online store and a 3rd-party shopping cart hosted on another domain, such as:
- www.example-store.com
- www.example-commerce-host.com/example-store/
Without cross-domain tracking, a user who comes to your online store and then proceeds to your 3rd-party shopping cart will be counted as two separate users, with two separate sessions of different durations.
Cross domain tracking makes it possible for Convert Experiences to see this as a single session by a single user and the session they started on the store site is continued through to the time spent on the shopping cart site.
However, since Cross Domain Tracking is a gray area under GDPR, when creating a new Project, the configurable option for disallowing Cross Domain Linking is now ON by default.
DPIA: We Take Changes Seriously
Data protection impact assessments (DPIAs) help organisations identify, assess and mitigate or minimise privacy risks with data processing activities. They’re particularly relevant when a new data processing process, system or technology is being introduced.
DPIAs also support the accountability principle, as they help organisations comply with the requirements of the GDPR and demonstrate that appropriate measures have been taken to ensure compliance.
Did you know that failure to adequately conduct a DPIA where appropriate is a breach of the GDPR and could lead to fines of up to 2% of an organisation’s annual global turnover or €10 million – whichever is greater?
As part of Convert’s GDPR Project, we developed guidance for team members and a template that’s used to carry out Data Protection Impact Assessments (DPIAs).
Download your copy of a pre-filled DPIA template here
Legitimate Interest Assessment (LIA): We Don’t Assume
Legitimate interest is one of six lawful basis set out in the GDPR to justify the processing of personal data.
And it sounds like the least work!
The legitimate interest basis is wide in scope and flexible. In layman’s terms it says that you can process data if processing that data is a no-brainer.
But there are so many ways to interpret it, that using legitimate interest is simply opening yourself to doubt and scrutiny. It is highly recommend that you resort to the legitimate interest basis when other bases (e.g. legal obligation or vital interest) are not available, or when legitimate interest is the most appropriate to use for the processing activity.
However, a proportionality assessment is required. Before using the legitimate interest basis, conduct the following:
- Purpose test: identity the legitimate interest;
- Necessity test: assess whether the processing is necessary to achieve that interest; and
- Balancing test: balance the legitimate interest against the individual’s interests, rights and freedoms.
We have conducted our own Legitimate Interest Impact Assessment (LIA) and have structured the consent options of our marketing touchpoints accordingly.
PCI-DSS for Secure Cardholder Data: Sensitive Information is Our Priority
We follow the principles and standard set out by the PCI Standards Council for storing and handling credit card information. More information is available here.
Though the PCI DSS is focused on securing payment cardholder data and the intent of GDPR is to protect EU residents’ personal data, a PCI breach is also a breach of personal data.
Consequently, under PCI DSS compliance we have always conducted annual reviews of cardholder data. This schedule of reviews thus gives us a framework that’s been used when implementing measures to comply with the GDPR.
In addition, we have invested in secure technologies for keeping cardholder data secure.
Beyond App Updates: GDPR Changes to the Convert Team
Legal:
We have updated our Privacy Policy and Terms of Service. We have added a new Cookie Policy. These updates went into effect for existing and new users and customers on the 25th of May 2018.
According to article 28, paragraph 4 of the GDPR, we sign a Data Processing Agreement (DPA) with all our European clients as a standard.
Sales:
We have made our sales processes GDPR compliant.
- LiveChat. If DNT is enabled for browsers, LiveChat doesn’t show up. We’ve removed all IP addresses from our LiveChat history.
- Contact Us Form. It was updated to be GDPR compliant.
- Request a Demo Form. It was also updated to reflect GDPR consent options.
- Re-permissioning Email Campaigns. We’ve run re-permissioning campaigns for all prospects who are in conversation with account executives to gather their consent for 1:1 assistance.
- Free Trial Form. It was updated to be GDPR compliant.
Marketing:
We have made our marketing processes GDPR compliant.
- Outbound Email Customers. We’ve stopped outbound campaigns in deference to GDPR.
- Re-permissioning Email Campaign. We ran re-permissioning campaigns to our entire database, getting granular consent to contact them with different types of communication.
- Newsletter Form. It was updated to be GDPR compliant.
- Lead Magnet Forms. They were updated to be GDPR compliant.
- Webinar Form. It was updated to be GDPR compliant.
- Free trial Form. It was updated to be GDPR compliant.
- Guest Post Form. It was updated to be GDPR compliant.
Human Resource (HR):
We trained our staff with seminars and all of them have a GDPR certificate covering basic knowledge.
Customer Support:
We trained our CS staff to respond appropriately to GDPR questions/tickets and data breaches.
Development:
Several guidelines were applied to our software development circle:
- Training (Developers were trained on Privacy and Security aspects)
- Design (All data oriented and process oriented design requirements were driven by GDPR)
- Coding (Developers use approved tools and frameworks, disabled unsafe functions and modules, and regularly carry out static code analysis and code review)
- Testing (We tested to ensure that data protection and security requirements were properly implemented)
- Before every release, an Incident Response Plan was established, and a full security review of the software was carried out. The release was then approved and all relevant data from the entire development process was archived.
- Maintenance (Convert is prepared to respond to incidents, personal data breaches, faults and attacks, and is capable of issuing updates, guidelines, and information to users and those affected by the software)
Policy Framework: Guiding Us to a Data Secure, Privacy Focused Future
To ensure consistent, high quality implementation and management of IT resources, processes and practices, we’ve defined a comprehensive framework of well-defined policies, procedures and standards.
In developing these IT policies, procedures and standards, we referenced the ISO 27000 series of standards which have been specifically reserved by ISO (International Standards Organisation) for information security matters.
Our IT policies are divided into two areas: policies pertaining to IT Security and Usage, and policies pertaining to Data.
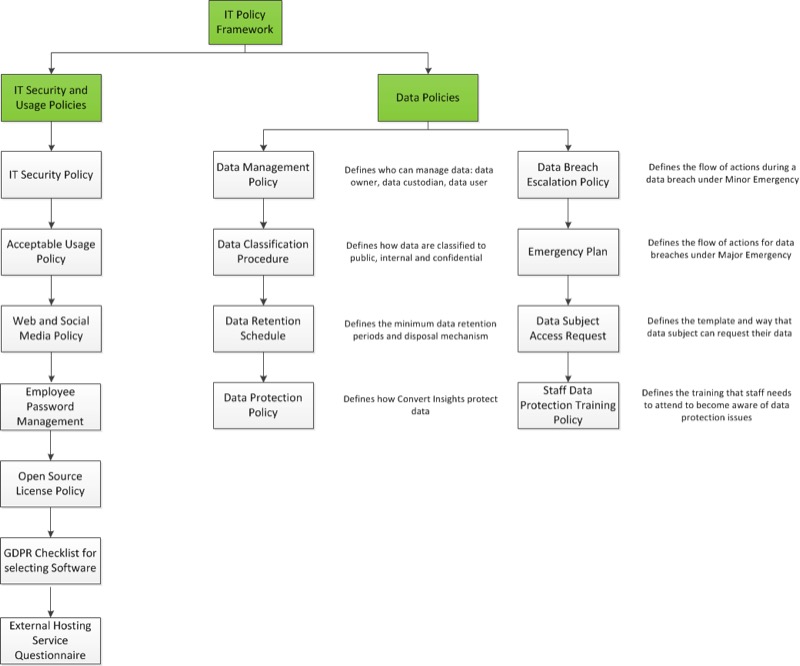
IT Security and Usage Policies:
The following policies and procedures provide clear guidance for IT Security and Usage:
- Privacy and Security Checklist for GDPR Compliance: GDPR requires Convert to protect the personal data of its customers and employees at all stages of the data processing lifecycle.With more businesses adopting and using cloud-based tools and software, complying with this requirement is a challenge. Businesses need to take different technology and legal aspects into consideration when looking for a service provider. This particular policy allows us to keep the most critical factors in mind while choosing service providers and vendors who align with our privacy focused approach.
- Open Source Software License Policy: The purpose of this Policy is to allow the Development circle to know which open source software license policies to accept when developing code.
- Employee Password Policy: The purpose of this policy is to make sure all Convert Insights resources and data receive adequate password protection. The policy covers all employees who are responsible for one or more account or have access to any resource that requires a password.
- Acceptable Usage Policy: This policy is designed to help Convert Insights staff understand their responsibilities when utilising, accessing or creating content with Convert Insights IT resources or networked services. It clarifies and defines (within reason) what Convert Insights deems as an acceptable use of these resources.
- Web and Social Media Policy: This policy clarifies how Convert Insights governs this digital estate and also provides guidelines for users when creating digital content on behalf of Convert Insights and guidelines around the use of official Convert Insights social media accounts.
- IT Security Policy: The objective of this security policy is to promote a culture that helps maximise the value of information through its efficient management and secure protection as well as safeguarding Convert Insights and the rights of staff and other parties who depend on the information.
- External Hosting Service Questionnaire: The purpose of this questionnaire is to ensure that third party Data Processors (in terms of the GDPR) have acceptable IT security and data privacy policies and procedures in place to minimise the risk of loss or exposure of Convert Insights personal data.
Data Policies and Procedures:
The following policies and procedures provide clear guidance on the acceptable, safe and legal way in which Convert Insights should use and manage data:
- General Data Protection Policy: This policy is a statement of Convert Insights commitment to protect the rights and privacy of individuals in accordance with the GDPR.
- Emergency Management Plan: The Emergency Management Team (EMT) will meet in response to a breach and decide if the Emergency Management Plan needs to be invoked. This team will act as an escalation point for serious incidents or breaches of policy related to data and resources.
- Data Management Policy: The purpose of this policy is to enable access to data and information held by Convert Insights, to the greatest extent possible while ensuring that it is protected from unauthorised use, access and breaches of privacy.
- Data Classification Procedure: The Data Management Policy requires Data Owners to classify their data according to its sensitivity and criticality. This procedure sets out how this classification is to be performed.
- Staff Data Protection Training Policy: This policy and any other documents referred to in it set out the training that Convert Insights staff will be provided with to ensure that all handling of personal data is compliant with the General Data Protection Regulation (GDPR).
- Data Access Request Procedure: The purpose of this procedure is to ensure that Convert Insights complies with the access request provisions of the General Data Protection Regulation and to enable individuals to submit data access requests where required.
- Personal Data Breach Escalation Policy: The purpose of these procedures is to provide a framework for reporting and managing data security breaches affecting personal or sensitive personal data held by Convert Insights. These procedures are a supplement to the Data Protection Policy which affirm its commitment to protect the privacy rights of individuals in accordance with Data Protection legislation.
To Convert GDPR is not an inconvenience.
It has reshaped the way analytics is used and has redefined its place in the world of optimization.
Analytics is no longer about hoarding prospect data in the hopes of finding elusive insights.
It is no longer about assuming personalization is the way to go.
Analytics and testing post GDPR is about minimalism. Making the most of data that can be processed in new and innovative ways.
If you want in on a tool that has your back through these privacy shifts – now and in the future, give us a 15 day, no obligations spin.
Try Convert Experiences for Free
Written By
Dionysia Kontotasiou
