A Look at the Colorado Privacy Act: Predictions on the Future of User Data Protection
This past July, Colorado passed the Colorado Privacy Act (CPA), making it the fourth state to enact comprehensive privacy legislation in the US, after California, Nevada, and Virginia.
While the CPA and similar laws will be subject to change as time passes, the question remains: should businesses begin working towards complying with each new individual law, or should they set up some sort of plan through which users’ rights remain protected no matter what happens in terms of policy changes?
With each state’s unique privacy regulations, it’s becoming increasingly difficult for companies to keep track of these changes, ensure compliance and avoid penalties.
To make this process easier, we will compare some recent examples from different states and offer insight into how they might affect business practices as well as future trends in user data protection.
In this blog post, we take a look at the Colorado Privacy Act and how it stacks up against other privacy laws, like Nevada’s SB20, Virginia’s CDPA, California’s CPPA and the most recent CPRA, and the European GDPR.
First, here’s a summary of all the key provisions of these laws:
| Key Provisions | Colorado CPA | Nevada SB220 | Virginia CDPA | California CDPA + CPRA | Europe GDPR | ||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Ability to Process | |||||||||||||||||||||||||||||||||||
| Data Minimisation | Yes | Yes | No | Yes | |||||||||||||||||||||||||||||||
| Permissible Purpose | Yes | Yes | No | Yes | |||||||||||||||||||||||||||||||
| Individual Rights | |||||||||||||||||||||||||||||||||||
| Right to receive notice of processing activities | Yes | Yes | Yes | Yes | Yes | ||||||||||||||||||||||||||||||
| Right to access personal data | Yes | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Right to data portability (i.e., data must be provided in a readily usable format, so it can be transferred from one entity/platform to another) | Yes | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Right to correct errors in personal data | Yes | Yes | No | Yes | |||||||||||||||||||||||||||||||
| Right to delete personal data | Yes | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Right to opt-out of behavioral advertising | No | Yes | No | Yes | |||||||||||||||||||||||||||||||
| Right to object to automated profiling and decision making | No | Yes | No | Yes | |||||||||||||||||||||||||||||||
| Right to non-discrimination for the exercise of these rights | Yes | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Right to opt-out of sales of personal information | Yes | Yes | Yes | Yes | No | ||||||||||||||||||||||||||||||
| Opt in or opt out for processing of sensitive information | Opt-in | Opt-in | Opt-out | Opt-in | |||||||||||||||||||||||||||||||
| Right to appeal denial of requests | No | Yes | No | No | |||||||||||||||||||||||||||||||
| Accountability/Governance | |||||||||||||||||||||||||||||||||||
| Data Protection Assessments | Yes | Yes | No | Yes | |||||||||||||||||||||||||||||||
| Security | |||||||||||||||||||||||||||||||||||
| Appropriate Data Security to Safeguard Information | Yes | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Breach Notification | Yes | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Data Transfers Outside EEA | |||||||||||||||||||||||||||||||||||
| Additional measures for international transfers | Yes | No | No | Yes | |||||||||||||||||||||||||||||||
| Transfers to Third Parties | |||||||||||||||||||||||||||||||||||
| Contractual Requirements in Service Provider Agreements | Yes | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Marketing | |||||||||||||||||||||||||||||||||||
| Consent for Adtech cookies | No | Yes | Yes | Yes | |||||||||||||||||||||||||||||||
| Consent obtained prior to direct marketing | Yes | No | No | Yes | |||||||||||||||||||||||||||||||
| Enforcement Agencies | |||||||||||||||||||||||||||||||||||
| Attorney General | Attorney General | Attorney General, CPPA | DPA | ||||||||||||||||||||||||||||||||
| Operative date | |||||||||||||||||||||||||||||||||||
| 1 July 2023 | 1 October 2019 | 1 January 2023 | 1 January 2020 / 1 January 2023 | 25 May 2018 | |||||||||||||||||||||||||||||||
Watch this video for more information on the differences between EU and US privacy laws and which privacy standards should be considered when performing A/B testing.
What Do All These Privacy Laws Have in Common?
The CPA is similar to other privacy laws like GDPR, California’s law, and Virginia’s. However, it doesn’t compare with Nevada since the latter only enacted a much more limited law regarding the sale of certain data collected online, so it is excluded from the comparison below.
- Data Processing Agreement — This is common among all privacy laws. Put simply, it means an organization needs to draft a legal template where it describes the personal data processing activities taking place when using a service or product. In short, it talks about how the data processing is going to happen, who will be responsible for what, and what security measures are going to be taken. We have prepared our template back in 2018 for GDPR, available here. With every new law, we update the template clauses to adapt to all new legal terms.
- A second commonality between privacy laws is that all of them require organizations to take appropriate technical and organizational measures to respond quickly and properly when consumers exercise their rights. What these rights are differs from law to law, as seen in the table above, but the measures remain the same.
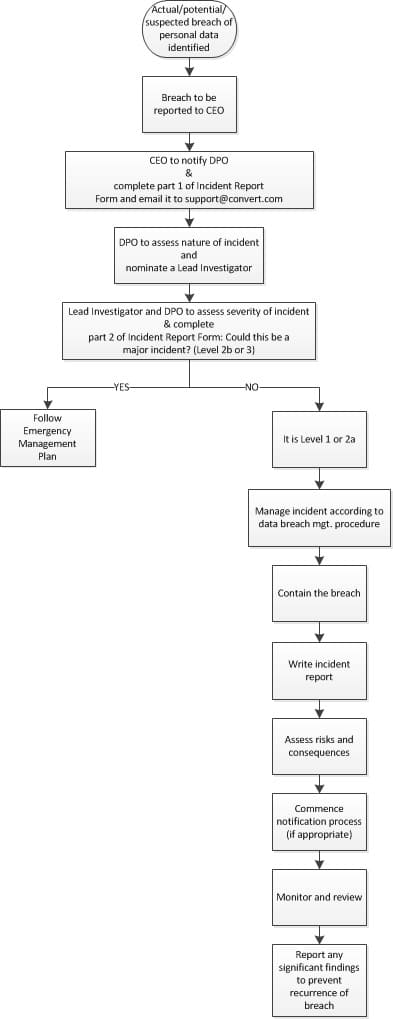
- Personal data breach notification is another common term present in the laws. A personal data security breach is any event that has the potential to affect the confidentiality, integrity, or availability of personal data held by an organization in any format.
Personal data security breaches can happen for many reasons, including:- the disclosure of confidential data to unauthorized individuals;
- loss or theft of data or equipment on which data is stored;
- inappropriate access controls allowing unauthorized use of information;
- attempts to gain unauthorized access to computer systems, e.g. hacking; records altered or deleted without authorization by the data “owner”;
- viruses or other security attacks on IT equipment systems or networks;
- leaving IT equipment unattended when logged-in to a user account without locking the screen to stop others from accessing information;
- emails containing personal or sensitive information sent in error to the wrong recipient.
- Another common requirement under GDPR, CCPA, VCDPA, and CPA is the process of conducting Data Processing Impact Assessments (DPIAs) for any new high-risk processing projects. A DPIA is the process of systematically considering the potential impact that a project or initiative might have on the privacy of individuals. It allows organizations to identify potential privacy issues before they arise and come up with a way to mitigate them. The GDPR first introduced mandatory DPIAs for those organizations involved in high-risk processing; for example, where new technology is being deployed, where a profiling operation is likely to significantly affect individuals, or where there is large-scale monitoring of a publicly accessible area.
For example, to exercise your right to access your personal data Convert is using, you must send a written request to [email protected]. In the request, mention that your request is being made in exercise of your right to access under the specific privacy law you are interested in. The DPO is required to respond to your written request. Be prepared to provide evidence of your identity, which the DPO should require of you to make sure that personal information is not given to the wrong person. The process above is specific to the GDPR, CCPA, CPA and is already documented on our Privacy page.
Similarly, if you want to close your Convert account, leave the service, and want a backup of all your Convert data, you may exercise your right to data portability. You can write an email to the same email address above, if the option to download the data is not immediately available, and ask the DPO for a backup of the data used across the service. The DPO must act on your written request.
In its GDPR Project, Convert developed guidance for staff and a template to be used to carry out DPIAs. You can find the template with the pre-filled screening questions here. This template has since been adapted to new US privacy laws.
But There Are Some Key Differences!
GDPR protects personal data. US laws mainly protect those consumers who choose to have their personal data protected.
- The debate on data vs consumer protection lays at the core of all these privacy initiatives. It’s also a key point that differentiates GDPR from all other privacy laws. With GDPR, personal data is protected throughout the various phases, from the collection, processing, storage, transfer to third parties. US laws make sure that the consumer is protected while they are online and using services, browsing, or testing products. This is why a company’s Privacy Policy cannot stay the same when a new law comes into force. New sections need to be added, to reflect new legal terms and provisions. Always consult with your lawyers to know exactly what to add to be compliant with each law.
- The laws also differ in the scope of the opt-in/opt-out regime. GDPR operates under an opt-in regime, meaning, European Union member countries do not collect any personal data from the visitor until they consent explicitly by checking a checkbox on the consent banner appearing on the site they are navigating. The opposite is happening in US-based publisher sites. Data can be collected until a visitor decides to opt-out of the data processing. California only operates under somewhat of a hybrid opt-out/opt-in regime. The CCPA allows an organization to collect consumers’ data by default, but also requires data collectors to provide privacy notices to consumers before data collection. The CPA, VCDPA are under a clear opt-out regime.
At Convert, we operate under an opt-in regime as we value transparency and visitors’ choices and we have adapted our User Experience to match its requirements. - Differences can also be seen in the rules of international data transfers. GDPR is again very strict with these transfers and allows them only when the recipient country has similar privacy regulations. It otherwise requires organizations to use standard contractual clauses or users’ consent. On the other hand, CCPA and VCDPA allow international data transfers worldwide until an incident occurs. Then, the organization is held responsible and fines apply. The CPA is somewhat lenient, requiring organizations to inform users/visitors when international data transfers occur but not restricting them.
At Convert, we adhere to the GDPR and provide the necessary transfer tools when requested (Standard Contractual Clauses are part of the contract our users are signing). - Finally, the laws have different response periods to privacy violations. The GDPR and the VCDPA give controllers or processors 30 days to react to privacy violations. The CPPA is permitted, but not required to offer a period to cure violations of the CPRA. The CPA must offer a 60-day response period.
Since Convert has not been part of any privacy violation, this was not easy to be tested, but we simulated such requests internally and found out that we can respond within 7-10 days. Quite impressive given the fact that many people and tools can be involved.
Is Your Company Prepared for the CPA?
Many of these laws have similar verbiage, so spotting the differences is quite difficult. However, we tried to make it clearer for you with this comparison above. To achieve compliance with these privacy laws, be prepared to spend lots of time reviewing them and consulting legal experts.
Thankfully, some measures universally apply to all of them. We have listed them in one of our previous articles, but here they are again to refresh your memory:
- Create and maintain a comprehensive data inventory, providing insight into both the types of data involved and the nature of processing activities.
- Ensure that sensitive data is segregated and managed without unnecessary risks.
- Implement a framework for conducting Data Protection Impact Assessments (DPIA).
- Assess the cybersecurity policies, practices, and controls in place to ensure they are consistent with industry-recognized standards.
- Enable consumers to opt out of the sale of their personal information (where applicable).
- Update public-facing privacy policies to, among other changes, pledge not to re-identify de-identified personal data and provide details on its data processing activities.
- Develop mechanisms for accepting, tracking, verifying, and honoring consumer requests to access, correct, delete, and opt-out personal data under the CPA.
- Ensure that your customer service employees have accurate knowledge of the regulations to satisfy consumer requests efficiently and predictably.
What Will the Privacy Landscape Look Like in the Next Decade?
Data privacy is emerging as a defining issue of this decade. This will be an ever-more privacy-sensitive world, where both businesses and individuals are becoming increasingly aware that there’s no longer any such thing as ‘private’.
The recent privacy laws taught us that these initiatives require extensive efforts and time to carefully plan, spot gaps in privacy mechanisms, and implement new policies, processes, and remediation efforts. So the data privacy landscape won’t change rapidly.
Though the future of privacy is largely unwritten, several trends are already shaping it in a variety of ways. Organizations that best navigate these trends over the next ten years will be more competitive than those that continue to just comply with new laws.
Let’s see what they are.
- Most consumers will be proactively protecting their personal data. We will see better privacy protection tools (the same way we now have privacy-invading tools). Organizations that do not adhere to these protections will risk losing their customers.
- Cross-border data transfers will get simpler. We won’t have to build local data kingdoms that cannot be entered by foreigners.
- Privacy customer experience journeys: new projects will be developed that align with the cultural and legal expectations of the privacy laws, as well as each company’s stance on data and technology ethics.
- Employee privacy culture: Human resources will use employee privacy programs that are aligned with the company’s data and technology values to develop a well-rounded privacy culture. Such a program might include an employee board that reviews and communicates privacy and ethical impact assessments for new technologies and data uses in the workplace.
A lot can change in 10 years, but then again, little can change too. Here at Convert, we’ve made respecting our visitors’ and users’ privacy part of our culture. Where will we be in 2030? By 2030, we see businesses who respect users’ privacy alongside regulators all working smoothly together without compromising on individual freedoms. This vision is what matters most to our team at Convert company and where we hope you will join us as well!
Written By
Dionysia Kontotasiou

Edited By
Carmen Apostu