Security Compliance
Security Compliance
Region-specific policies
Privacy Shield
Convert Insights Inc. is Privacy Shield compliant. More information about the steps we’ve taken can be found here.
General Data Protection Regulation (GDPR)
Convert Insights Inc. is GDPR compliant. See the Convert GDPR Company Page for more information about the steps we have taken to reach compliance as well as our roadmap for making Convert Experiences GDPR compliant.
Data Protection Agreement (DPA)
We are able to sign a Data Processing Agreement (DPA) for compliance with the European Union’s Data Protection Directive (EU DPD–sometimes called “model clauses”). We have aimed to make this as self-service as possible and have provided a GDPR-compliant DPA for download here.
Data Privacy Impact Assessment (DPIA)
A new requirement under GDPR is the process of conducting Data Processing Impact Assessments (DPIAs) for any new high-risk processing projects. Convert Insights Inc. developed guidance for staff and a template to be used to carry out DPIAs. You can find the template with the pre-filled screening questions here.
Legitimate Interests Assessment (LIA)
We have conducted a legitimate interests assessment (LIA) and kept a record of it, to ensure that we can justify our decision. You can access it here. We keep our LIA under review and repeat it if circumstances change.
Data Subject Access Request (DSAR)
Information on how to submit a GDPR Data Subject Request can be found here. The DSAR form is accessible here.
Company-specific Policies and Procedures
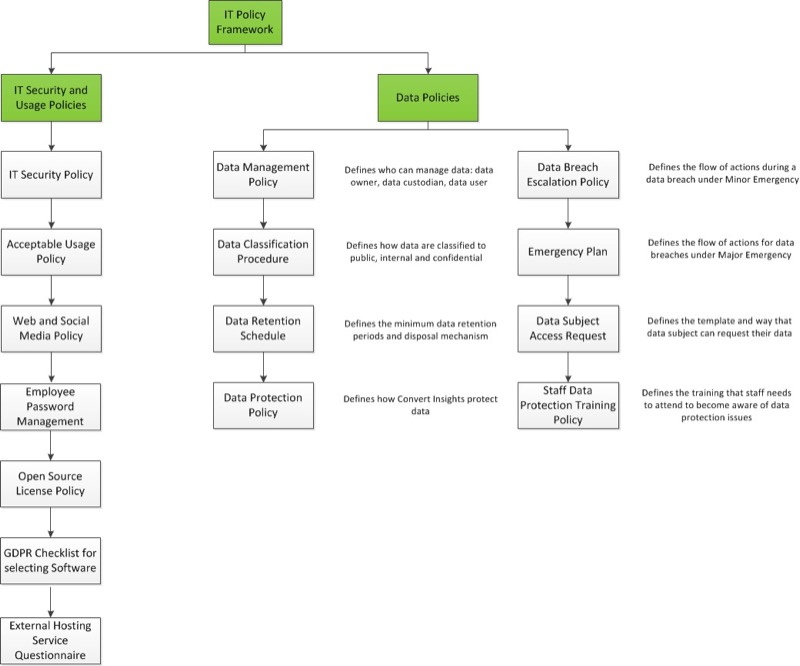
The following IT policies have been developed to facilitate and ensure consistent, high-quality implementations and management of Convert Insights Inc. IT resources and information.
IT policies are divided into two areas: policies pertaining to IT Security and Usage, and policies pertaining to Data. Should you be interested in accessing any of these policies, contact us at [email protected].
Certifications
SOC
Convert Insights Inc. isn’t itself SOC compliant, but our datacenter providers are (AWS/Hetzner). Customers interested in SOC reports concerning the cloud infrastructure providers utilized by our services can obtain the reports directly from the respective providers.
PCI-DSS
Convert Insights Inc. follows the principals and standard set out by the PCI Standards Council for storing and handling credit card information. More information is available here.
HIPAA Non-Compliance
Customers acknowledge that Convert Insights Inc. is not a Business Associate or subcontractor (as those terms are defined in HIPAA) and that the Convert Insights Inc. Services is not HIPAA compliant. “HIPAA” means the Health Insurance Portability and Accountability Act and related amendments and regulations as updated or replaced. “Regulated Data” includes HIPAA-regulated data and data covered under the Gramm-Leach-Bliley Act (or related rules or regulations) as updated or replaced.
ISO 27001
Not specifically. We opted to spend our time and collective years of experience and knowledge making the product secure and useful, rather than doing a certain set of tasks to check off boxes to get a certification like ISO 27001.
Security
Servers and databases
We use Amazon Web Services (AWS) for our production servers and databases. You can read about how seriously AWS takes security on the AWS website. AWS employs cutting-edge data security measures, as well as physical access restrictions at server locations. We also use Hetzner Online GmbH for the login site to be compliant with the GDPR.
Security and Vulnerability Testing and Prevention
In Progress
OWASP Security Risks and Actions
The OWASP Top-10 covers the most critical Web application security risks. You can access here our OWASP evaluation.
Bug Bounties
We are interested in actual security, so if someone reported
what we felt was both:
- A serious vulnerability (and not just a low/zero-risk XSS), and
- Discovered during routine use of the application as an actual user – not via a pen test, which would have been unauthorized
…we would look kindly on that and might consider sending a thank-you bonus.